Yesterday, FireEye/Mandiant announced that a “highly sophisticated state-sponsored adversary stole FireEye Red Team tools.” We agree with a Microsoft spokesperson who was quoted as saying “This incident demonstrates why the security industry must work together to defend against and respond to threats posed by well-funded adversaries using novel and sophisticated attack techniques.”
Stamus Networks and our partners are already working together to ensure a swift and thorough response. Here are the steps we are taking:
Last night our partner Proofpoint published a set of 42 signatures for their ETPro Suricata ruleset. These contain specific detection mechanisms for the offending tools. The ETPro team is working as we write this to develop even more detection signatures for these stolen tools.
For users of the Stamus Network Detection (Stamus ND) and Stamus Network Detection and Response (Stamus NDR) who subscribe to the ETPro feed, these new signatures will be activated by default at your next scheduled update. You may find these in your system by searching for “[fireeye]” signatures from the Enriched Hunting user interface.
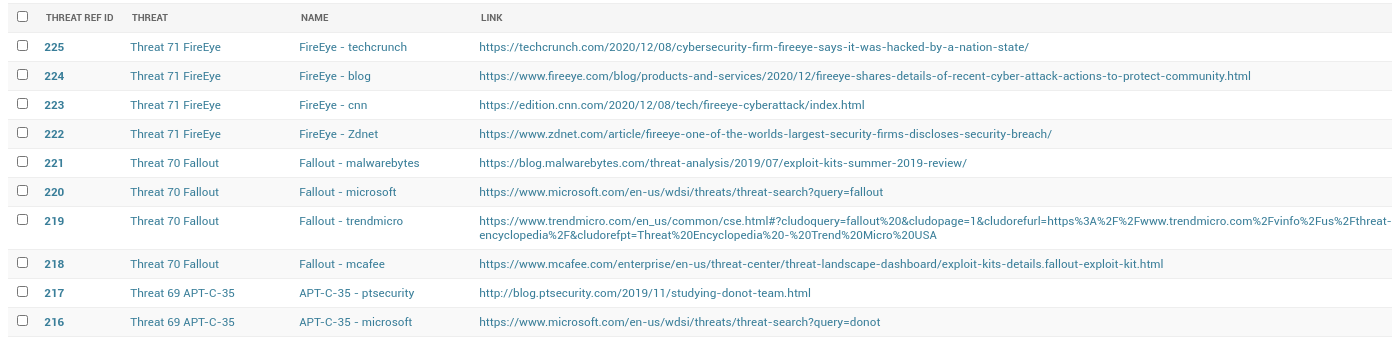
Figure 1. ETPro rules for detecting FireEye tools in Stamus ND/NDR
For those who are using SSP for proactively threat hunting, Scirius Enriched Hunting may be configured to auto classify "fireeye" alerts, allowing for rapid identification and classification of these events.
Finally, the Stamus Networks Threat Research team have developed a dedicated threat named “FireEye” and a set of associated threat vectors for Stamus Security Platform which will identify a “Stamus Threat” if any of your assets are attacked by the stolen tools. This new threat intelligence is available immediately and will be delivered to all customer systems that are configured for automatic updates.
Stamus Security Platform (NDR) represents the state of the art in network security. NDR represents the evolution of network threat detection tools that aims to replace the capabilities of intrusion detection (IDS) and network security systems (NSM).